lifetech
Information Security: Products and Services.
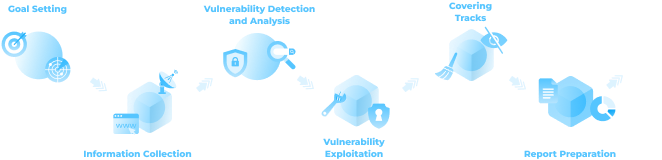
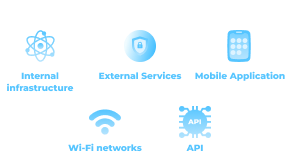
Audit and Penetration Testing
Design of Information Security Systems
Development of Information Security Systems
Certification
Operation
CONTACT US
Cybersecurity services
Our advantages
Experience with Complex Telecom Infrastructures
Extensive experience with complex and diverse IT infrastructures of a telecom operator infrastructures of a telecom operator
In-House CDC Certification
Successful certification project for the CDC, delivered fully in-house without external contractors, covering both process development and technical domains, including reverse engineering and penetration testing.
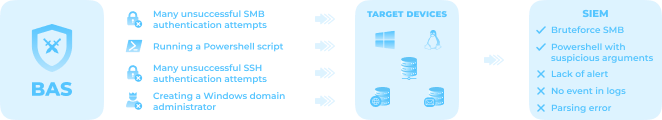
InHouse Built Visibility Solutions
Development of proprietary cybersecurity solutions and services (BAS – practical assessment of SIEM effectiveness; ASM – improving visibility of the organization’s external attack surface).
Owner of Critical Informatization Infrastructure
Compliance with regulatory requirements for the design, implementation, and annual audit of an information security system for a Critical Informatization Infrastructure.
Enterprise SIEM Deployment and Support
Commercial experience in the implementation and support of SIEM systems for large enterprise clients.
In-house expertise in the deployment and integration of security solutions
In-house expertise in the deployment, integration, configuration, maintenance, and update of security solutions from Kaspersky and other vendors within a certified CDC.
Cross-Industry Security System Design
Experience in the design and development of information security systems across multiple industries.
Contact us.
Or write here
info@lifetech.by